Learn extra at:
In context: As sickening as it’s to confess, knowledge breaches have grow to be a truth of life. We can’t go greater than a month with out one firm or one other saying {that a} hacker or poor safety hygiene left its purchasers uncovered. As annoying as that’s, it is much more irritating when the corporate tries to cover the intrusion.
Earlier this month, a risk actor going by Rose87168 claimed to have breached Oracle Cloud’s federated SSO servers and exfiltrated round 6 million information, affecting over 144,000 Oracle purchasers. The hacker offered an inner buyer checklist and threatened to promote the information until purchasers paid to take away their knowledge from the trove, which included single sign-on credentials, Light-weight Listing Entry Protocol passwords, OAuth2 keys, tenant knowledge, and extra. Rose87168 has additionally solicited assist from the hacking neighborhood to crack the hashed passwords in commerce for among the knowledge.
A day after the risk actor posted a small pattern of the information, Oracle informed Bleeping Laptop there was no breach of its cloud service. Upon Oracle’s denial, Rose87168 started leaking “proof” to the media and safety researchers. Safety group Hudson Rock and specialists at CloudSEK concluded that the information and credentials are official.
CloudSEK stated that the hacker seems to have used a zero-day vulnerability (CVE-2021-35587) in an entry supervisor software program associated to Oracle Fusion Middleware to breach Oracle Cloud techniques with out authentication.
“Fairly loopy Oracle simply denied this leak, which has been verified independently by many cybersecurity companies,” Hudson Rock CTO Alon Gal posted on LinkedIn on Monday.
Trustwave SpiderLabs additionally reviewed the proof and concluded that the information was positively from Oracle Cloud servers.
“The dataset described by the offered headers represents a extremely detailed and delicate person listing, doubtless extracted from a company Identification and Entry Administration system or HR-integrated listing comparable to Microsoft Lively Listing, Oracle Identification Supervisor, or the same platform,” Trustwave’s safety advisory learn.
The safety agency additionally confirmed that the cache included personally identifiable info comparable to first and final names, full show names, electronic mail addresses, job titles, division numbers, phone numbers, cellular numbers, and even dwelling contact particulars. The hacker additionally uploaded a recording of an inner Oracle assembly.
“Such knowledge in a leaked format poses extreme cybersecurity and operational dangers to the affected group,” Trustwave added.
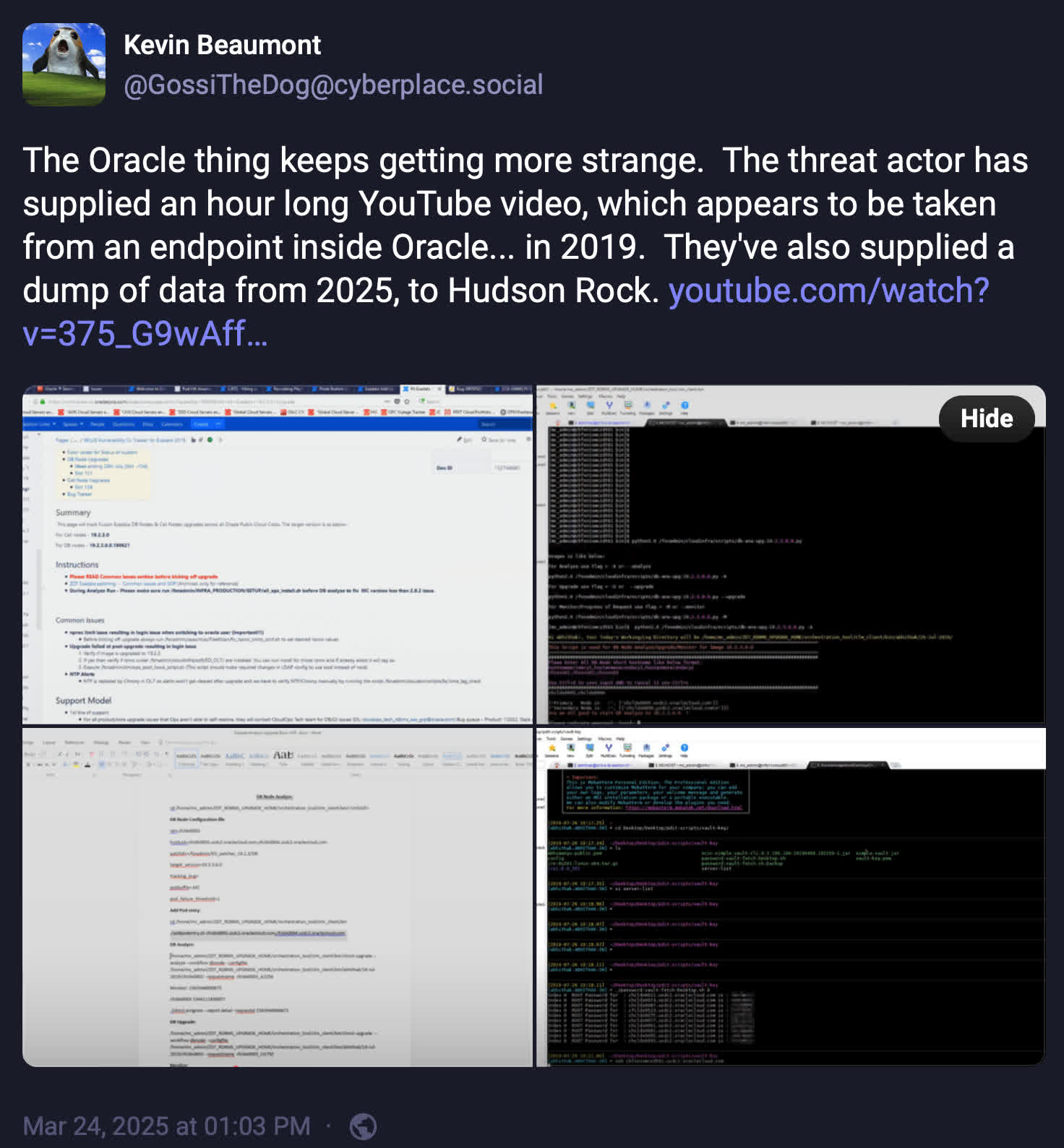
Moreover, cybersecurity specialist Kevin Beaumont famous that Oracle “rebadged” legacy Oracle Cloud providers as “Oracle Traditional.” He claims that the corporate’s cautious wording in its response is a technically factual however disingenuous denial. The corporate seems to be making an attempt to situate the incident as insignificant or that it did not leak present Oracle Cloud information. For reference, right here is Oracle’s assertion to Bleeping Laptop:
“There was no breach of Oracle Cloud. The revealed credentials should not for the Oracle Cloud. No Oracle Cloud clients skilled a breach or misplaced any knowledge.”
Beaumont discovered the repetitious use of “Oracle Cloud” suspicious as if it could be organising Oracle Traditional to take the autumn. Nonetheless, whatever the age of the breached servers, CloudSEK confirmed by way of a few of its purchasers that the information was correct and present. This conclusion debunks any notion that the breach was insignificant or contained outdated info.
Regardless of a number of researchers reporting that the information breach is severely regarding, Oracle has remained silent because it denied the assault. Beaumont says the corporate’s silence is irresponsible. Likewise, Gal referred to as Oracle’s lack of transparency and steerage “loopy.” Missing any recommendation from the corporate, Gal directed affected clients to CloudSEK’s mitigation suggestions to attenuate any potential harm from the leak.